Internal Software & Tools
Atlan Digital R&D develops innovative technologies that power modern adversary simulation, CNO, and EDR evasion research.
Command and Control Framework - Turul
Turul C2 is a command-and-control framework coupled with Turul GAN. Our initial lab post, Malware GAN & ATP: Detailed Introduction, started this process and captured the early research direction.
Building on MalwareGAN, we rebuilt a leading open-source C2 across the backend, beaconing, and frontend, then validated changes in lab and controlled client exercises to improve reliability and usability.
Turul reduces on-host noise and telemetry while keeping operator control over beaconing, post-exploitation, and enumeration; post-exploitation modules are decoupled from the beacon for targeted delivery. With Turul GAN enabled, implants and modules become function-preserving, unique variants generated at machine speed rather than manual obfuscation, and the approach remains a work in progress for responsible, repeatable evaluation.

TURUL C2
Internal use and ongoing development
Turul is currently at v1.0, but it is a fully functioning command-and-control framework. It integrates the Turul GAN server API to generate function-preserving C# variants of implants and post-exploitation modules before delivery, and includes encrypted beaconing, steganography, built-in evasion, malleable profiles, and more.
Visit our Turul C2 documentation for the full project introduction and current development details.
Turul C2 docsTurul GAN - Evasion as a Service
TURUL GAN
Turul GAN is a code transformation engine that uses a generator/discriminator loop to produce function-preserving C# variants that score as benign under ML-based static analysis. It also introduces junk behavioural routines today (rudimentary), with a roadmap toward a tailored runtime engine that mimics benign reads across numerous post exploitation TTPs. It runs as a service behind Turul C2 for on-demand transformations and can also ingest the SharpCollection toolkit, transforming most modules.
Static Code Evasion
Transforms C# code using GAN-guided, semantics-preserving variants to bypass static analysis, including most SharpCollection modules.
Basic Runtime Obfuscation
Introduces lightweight runtime noise to reduce deterministic patterns.
C2 Framework Agnostic
Integrates with other C# C2 frameworks (e.g., Covenant, SharpC2) for red teaming and CNO/CNE workflows.
EDR Coverage
Turul is validated against leading enterprise EDR and XDR platforms. Specific compatibility details are shared under NDA as part of a demo engagement.
API & Pipeline
Turul GAN exposes a REST API so operators can automate transformations inline with red team and CNO workflows — including CI/CD pipeline integration and on-prem deployment for air-gapped environments.
- Parallel transformation jobs
- Optional code signing
- Git-triggered pipelines
- On-prem deployment
- Full API documentation available on request
Turul GAN in Practice
Current position
Turul GAN was NATO DIANA shortlisted and has been engaged with defence sector stakeholders. The capability sits in a commercial grey zone and we are still shaping its long-term path. In the meantime, it strengthens our advanced penetration testing and adversary simulation work, and we can support controlled engagements that use Turul C2 + Turul GAN to stress-test environments or generate adversarial samples for defence-evasion validation. For enquiries, reach out here.
Watch Turul in Action
Turul GAN and Turul C2 demos
Brief videos of Turul GAN and Turul C2 and evasive transformations.
Turul GAN Demo
CFG Segment Viewer
Conceptual Overview of Turul and GANs
This overview presents what the GAN does, why it helps to test defences, and the roadmap toward Phase 2.

Conceptual Overview of Turul and GANs
This overview presents what the GAN does, why it helps to test defences, and the roadmap toward Phase 2.

Initially, we set out on the GAN project some years ago, however owing to budget constraints, the process took much longer than expected to get to a stage 1 which we can release to the Red Team and CNO community.
With Turul GAN, there are two things at play here that we will delve into: one aspect is the code transformation, and the other aspect is why this approach was taken and also the long future vision.
Let us Begin with the Why?
Red Teams and CNO operators must devote significant time to developing evasions both behaviorally and statically, and the EDRs evolve as time goes by addressing these evasions. Most of these methods revolve around blinding the EDR's ML models. Techniques are discovered that allow for a wide range of methods that essentially limit the data that is being delivered to the ML model within the EDR. Whether this is encrypting and unencrypting your shellcode in memory, or doing some kind of esoteric process injection, or hiding behind an AppDomain injection, the core focus is to hide the malicious code that you are deploying away from the machine learning model that is trained on the signatures of these malicious codes.
At points throughout the lifecycle of the execution of typical Red Team strategies, the shellcode or binary that is performing your malicious actions is being exposed to the EDR ML model, and the name of the game is to not be seen.
This creates a cycle whereby you need to constantly find new ways to blind the EDR, which is resource-intensive. Our solution is a first-stage step in limiting the process of having to find these evasions and directly engage the ML model itself and offload the development of evasions to algorithms.

How Can This Be Approached?
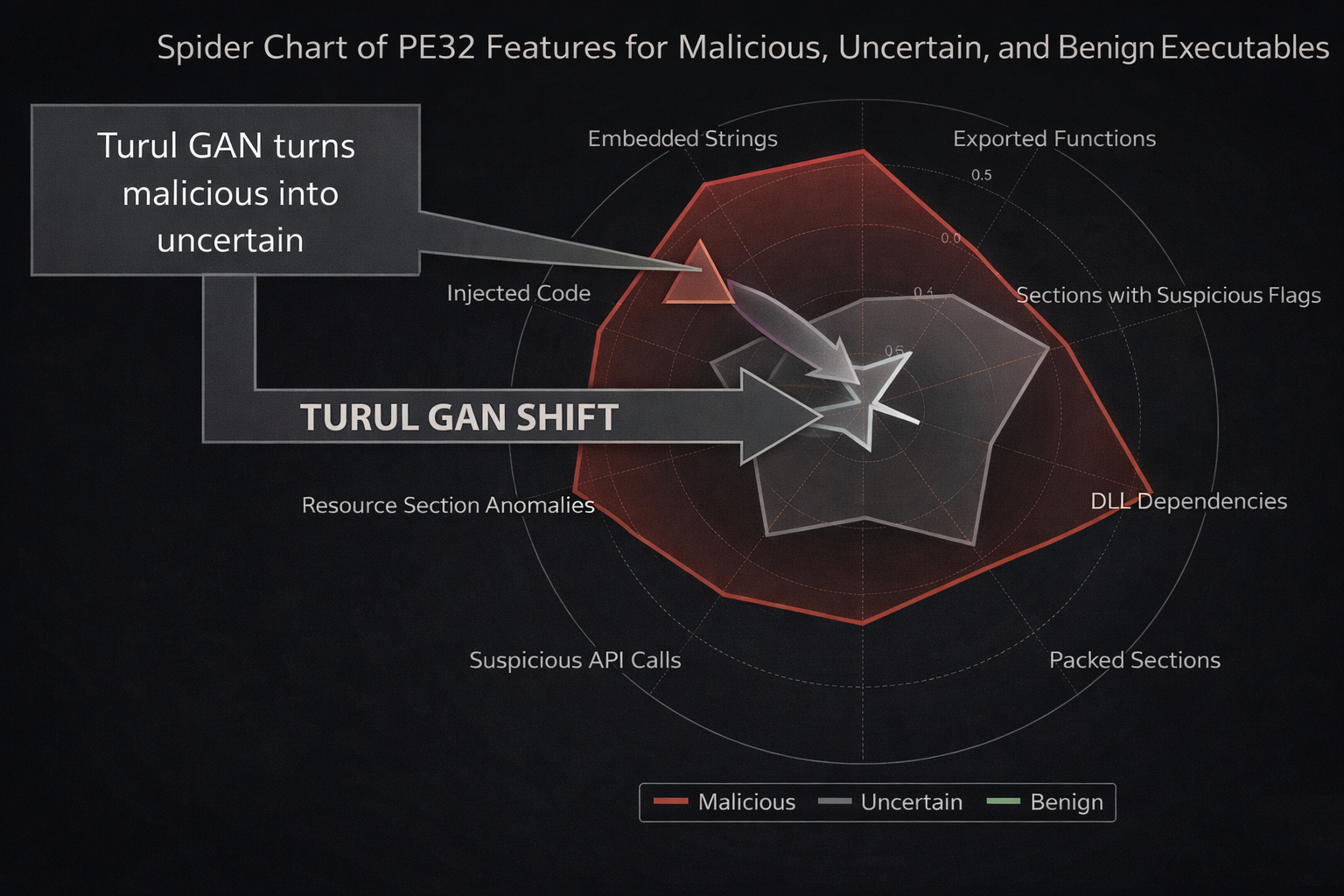
If you think about the challenge that EDR developers face, one is that they must deal with limiting false positives, and so there are a wide range of code bases that they are trained to ignore. This evaluation will be based on a P-value threshold whereby some code at a certain threshold will be deemed benign, some code will be deemed uncertain, and some code will be deemed malicious. These kinds of values are derived from the machine learning training process where they take hundreds of thousands of malicious samples, try to learn their features, and offset this against false positives whereby non-malicious code is not inadvertently flagged.
This process obviously works both behaviorally and statically, and they have to make trade-offs in the cases where some code may be very close at once to normal code, and whereas some code maybe close to obviously malicious.
This presents challenges to the offensive security community, given that most of the tools in use are heavily signatured and the machine learning models are well-trained to evaluate unknown code that is also malicious in intent.
Engaging with ML Models Directly
To bypass EDRs effectively, we must shift our focus from simply obfuscating code to actively influencing how the ML model perceives it. If we understand the decision boundaries that an EDR model uses to classify threats, we can generate code that falls into an uncertain or benign category.
This is the space where Turul GAN seeks to work in. Instead of relying on traditional obfuscation, our system uses a generative adversarial network (GAN) to transform malicious code in a way that maintains functionality while appearing statistically benign to an ML-based EDR.
At a high level, Turul GAN operates in a two-step process:
- Code Transformation:
- The generator network modifies an input sample (e.g., implant, loader) to evade detection.
- The goal is to reshape the code's statistical and behavioral signature while ensuring it remains operational.
- Adversarial Evaluation:
- The transformed code is tested against real-world offline EDR models.
- Feedback is used to refine the transformation process.
The conventional method of creating evasions requires extensive testing, reverse engineering, and manual tweaking. While effective, it is inefficient in the long term. Machine learning, on the other hand, is trained on vast datasets and constantly adapts, so why not fight fire with fire? However, we are only at Phase 1.
Phase 1: Rule-Based Transformation
Turul GAN currently operates on a rules-based architecture, leveraging block segmentation and semantic-preserving transformations to modify code at a structural level while ensuring functionality remains intact.
Payloads are broken into functional blocks, each of which can undergo controlled modifications while preserving execution. The result is a large space of unique variants — each functionally identical, each statistically distinct.

Why Phase 1? The Real-World Challenges of GANs in Code Transformation
GANs Struggle with Code Semantics
Traditional GANs excel at generating unstructured data like images or text but struggle with structured code. Code execution is binary, it either works or it does not. Even a minor unintended modification can result in syntax errors, logic failures, or even entirely broken binaries.
In image generation, an ML-based GAN can generate a blurry or slightly distorted face, and it is still a face. In code generation, even a misplaced bracket or minor transformation can completely break execution.
Thus using a purely ML-driven GAN from the start could generate malformed C# payloads that do not execute correctly.
Maintaining Execution Integrity
Unlike in adversarial image generation (where "fooling" a classifier is the only goal), in Red Team operations, code must execute correctly while remaining evasive. A GAN generating novel C# transformations would need additional constraints to preserve function and syntax, a challenge that traditional GANs are not designed to handle.
Solution in Phase 1: Rule-based logic ensures that every transformed variant remains semantically identical to the original, avoiding execution failures. Block-based segmentation provides controlled modifications that maintain structural integrity.
GANs Lack Awareness of C# Compilation Rules
Neural networks do not inherently understand C# syntax, dependencies, or compilation constraints. Without strict training constraints, a GAN attempting code transformations might produce outputs that do not compile or cause unintended runtime errors.
Solution in Phase 1: Instead of blindly learning transformations, rule-based logic enforces constraints that guarantee valid outputs. Every change adheres to predefined syntax-safe modifications.
One of the biggest challenges in ML-based GAN training is the need for a large, high-quality dataset.
A GAN that modifies C# payloads would need thousands (or millions) of labeled examples of transformations that evade detection while preserving functionality. By starting with Phase 1, we generate structured, rule-based transformed samples, creating a clean dataset for training a future ML-driven GAN.
Phase 2: Toward Adaptive ML
While rule-based transformations provide strong coverage, they remain constrained by predefined logic. The next phase moves toward a hybrid model — one that learns from real-world detection feedback rather than relying solely on fixed rules. The specifics of that architecture are kept internal.
What Comes Next:
We will introduce, with videos, the current use cases for the technology. These range from powering other C2s to acting in a CICD pipeline of offensive tools, to generating unique variants of loaders.
We will also introduce how behavioral detections are handled currently, and the future situation there.
Our goal is to replace the need for any reverse engineers and human evasions developers long term, and have achieved a working solution that goes some of the way there currently in one code language.
If you are interested in more please reach out to us.
Research Timeline
A seven-year R&D trail — from early GAN experiments at Hunnic Cyber to a NATO DIANA-shortlisted evasion engine and a full C2 platform.
Research Timeline
A seven-year R&D trail — from early GAN experiments at Hunnic Cyber to a NATO DIANA-shortlisted evasion engine and a full C2 platform.
-
2019
GAN Research Begins — Hunnic Cyber
Early investigation into using machine learning to challenge ML-based detection — exploring whether generators could outpace signature and behavioural defences.
-
2020
Early GAN Experiments, SharpML & ML for Red Teams Begins
First internal GAN prototype — academic in nature, exploring how adversarial ML could be applied to detection evasion. SharpML released: ML-driven credential hunting on enterprise networks. Work began on the ML for Red Teams course; first half recorded.
-
2022
First Public Research Output
Published four lab posts documenting earlier tradecraft across malware development, pre-phishing recon, and the SharpML work from 2020.
-
2023
MalwareGAN Formalised — ML for Red Teams Released
GAN-based evasion research formalised and documented. Decision taken to stop releasing offensive tooling publicly after earlier open-source work was identified in use by ransomware operators. ML for Red Teams course completed and released.
-
2024 Q1
ML for Red Teams — Revised Release
ML for Red Teams re-released with minor updates and modifications, keeping course content current with the evolving threat landscape.
-
2024 Q2
Research Expands Beyond EDR
Coverage extended across the full detection stack — endpoint, network, and extended detection and response. Research moved from point evasion toward full kill-chain awareness.
-
2024 Q3
Surrogate Modelling of Enterprise Detection
Research into understanding how leading enterprise detection platforms make decisions — building internal models of their behaviour without access to their internals.
-
2024 Q4
Turul C2 + Turul GAN — NATO DIANA Shortlisted
Turul C2 developed: a full command-and-control framework built for adversarial ML research engagements. Turul GAN brought into a single platform alongside it. Shortlisted for the NATO DIANA accelerator programme.
-
2025
Defence Engagement & Next Phase Planning
Turul GAN engaged with defence sector stakeholders. Next phase of research scoped: moving toward more adaptive, generative approaches that go beyond the current platform.
-
2026
ML for Red Teams Training + Continued R&D
ML for Red Teams continues to grow — transferring adversarial ML knowledge to the practitioner community. The internal research stack has expanded significantly; the pipeline now extends well beyond the C2 and GAN. Further tooling in development behind closed doors.
ENQUIRIES
Whether you represent a corporate, a consultancy, a government or an MSSP, we’d love to hear from you. To discover just how our offensive security contractors could help, get in touch.
General Enquiries
+44 (0)208 102 0765
enquiries@atlan.digital
86-90 Paul StreetLondon
EC2A 4NE
New Business
Tom Kallo
+44 (0)208 102 0765
tom@atlan.digital
